Table of Contents
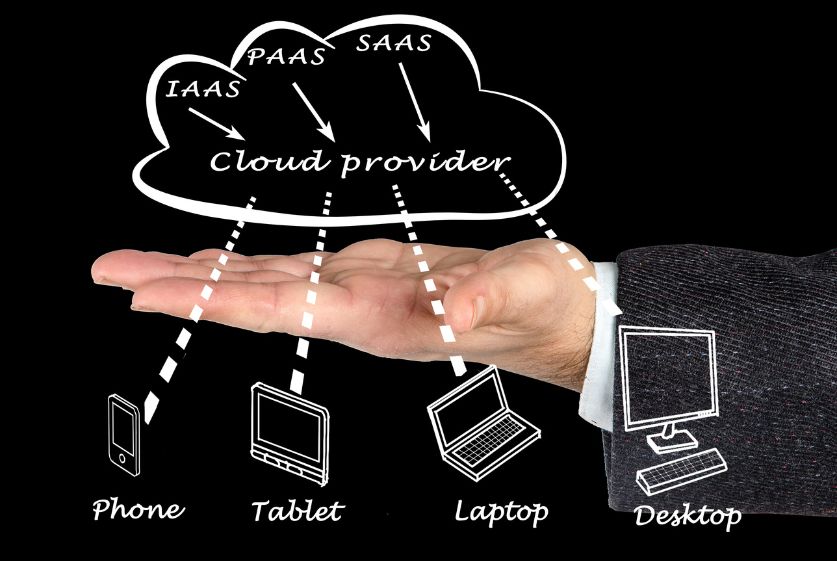
Cyber Security as a Service (CSaaS) refers to outsourced security solutions delivered through the cloud on a subscription basis. Instead of building and managing on-premises security tools and infrastructure, organizations can leverage Cyber Security as a Service provider to handle key aspects of their cybersecurity programs.
Defining Cyber Security as a Service
Cyber Security as a Service solutions deliver security capabilities remotely through the cloud, eliminating the need for on-premises hardware and software. Services may include:

- Endpoint protection
- Data loss prevention
- Intrusion detection and prevention
- Security monitoring
- Identity management
- Incident response
By relying on Cyber Security as a Service, organizations can reduce costs, access top security talent, and alleviate the burden on in-house IT and security teams.
Benefits of Cyber Security as a Service
The main benefits of Cyber Security as a Service include:
- Cost savings – No upfront investments in infrastructure and software licenses. Pay based on usage.
- Instant deployment – Quick and seamless rollout of advanced security controls.
- Scalability – Ability to easily adjust capacity on demand.
- Top security expertise – Tap into providers with dedicated security operations centers and skilled staff.
- Consolidated view – Centralized monitoring and management of security controls through a single pane of glass.
Challenges of Adopting Cyber Security as a Service
Some key adoption challenges remain:
- Integration complexity – Connecting Cyber Security as a Service tool with existing security systems and infrastructure.
- Compliance risks – Ensuring providers meet necessary regulatory requirements.
- Cloud dependencies – Introducing new availability and outage risks.
- Lack of control – Relying on the vendor for security configurations and patching.
Key Drivers Behind the Growth of Cyber Security as a Service
Several factors are fueling rapid growth in the Cyber Security as a Service market:

Increasing Cybersecurity Threats
The sophistication and frequency of malware, ransomware, and phishing attacks continue to rise. Outsourcing security allows organizations to arm themselves with advanced protections.
Complexity of In-House Security Operations
Managing a full in-house security stack has become overwhelmingly complex. Cyber Security as a Service simplifies security operations and monitoring.
Cost Savings from Outsourcing Cybersecurity
Between infrastructure, tools, and specialized staff, in-house security investments are substantial. CSaaS provides immediate savings from outsourcing these expenses.
Components and Capabilities of CSaaS Solutions
Cyber Security as a Service encompasses a wide variety of security offerings, including:
Endpoint Protection
Secures workstations, laptops, tablets, and mobile devices from malware, exploits, and data exfiltration.

Data Loss Prevention
Prevents sensitive data from leaving corporate networks and systems.
Security Information and Event Management (SIEM)
Collects, analyzes, and correlates security telemetry from across the enterprise infrastructure.
Identity and Access Management
Governs access to applications and resources based on user identities and roles.
Vulnerability Management
Scans infrastructure, endpoints, and applications to discover security flaws and misconfigurations.
Cloud Workload Protection
Locks down public cloud workloads across Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) environments.
Managed Detection and Response
Proactively hunts for threats, investigates incidents, and performs containment and remediation through a team of security analysts.
Selecting the Right Cyber Security as a Service Provider
With hundreds of vendors offering Cyber Security as a Service, it’s critical to choose your partner carefully based on:
Solution Sophistication and Scalability
Look for technically advanced offerings that can grow with your organizational needs over time.
Industry Expertise
Prioritize vendors with experience serving clients in your specific vertical and compliance requirements.
Flexible Pricing Models
Opt for subscription models over multi-year contracts to maintain budgetary flexibility.
Implementing and Integrating Cyber Security as a Service
Follow best practices when deploying Cyber Security as a Service:
Performing Due Diligence
Conduct ample research, ask detailed questions, and request demos during the vendor selection process.
Ensuring Smooth Integration with In-House Systems
Define technical requirements for integrating on-premises infrastructure and data flows with Cyber Security as a Service offering.
Managing Multiple Vendors
Unified dashboards can provide consolidated visibility across tools from disparate providers.
The Future of Cyber Security Services
Looking ahead, key developments will shape the continued evolution of Cyber Security as a Service:
Incorporating Artificial Intelligence and Machine Learning
Automating threat identification, investigation, and response will be a prime focus area.

Convergence with Other Managed Security Services
Integrations between cloud security, endpoint detection, and response, managed SIEM, and other offerings will deepen.
Increasing Cloud Adoption
As more workloads shift to the cloud, securing cloud-based assets with cloud-delivered security will gain prominence.
Conclusion
Cyber Security as a Service enables organizations to efficiently address pressing security challenges through cost-effective, cloud-based solutions. Key highlights include:
- Prioritizing threat protection over in-house tool management
- Leveraging security vendor expertise and resources
- Reducing infrastructure costs while gaining capabilities
- Selecting offerings aligned to technical and business needs
- Deploying CSaaS alongside existing controls as a force multiplier
With powerful motives driving adoption, Cyber Security as a Service is poised to continue its rise as a critical component of enterprise security programs.
FAQs
Q: What are the most commonly outsourced cybersecurity functions?
A: Endpoint protection, email, and web security, data loss prevention, security awareness training, and vulnerability management are among the most commonly outsourced areas. SIEM, identity management, and cloud workload security are also seeing increased adoption via CSaaS models.
Q: Is it safe to have an external provider handle security monitoring and management?
A: Reputable CSaaS providers invest heavily in compliance, data security, infrastructure resilience, and talent. Leading analysts often find security maturity levels higher among top vendors compared to average internal IT teams.
Q: How does CSaaS differ from managed security services?
A: Managed security services involve outsourcing security operations and technology management to a third-party provider. CSaaS delivers equivalent functionality exclusively through the cloud rather than on-premises solutions.
Q: What industries are currently driving most CSaaS adoption?
A: Highly regulated sectors like financial services, healthcare, and the public sector are driving considerable CSaaS adoption. Acceptance is broadening across manufacturing, retail, energy, education, and most major industries.
Q: Is it difficult to switch or terminate CSaaS providers?
A: Providers strive for seamless transitions between contracts. Some data and configuration migration may be required when switching vendors. Well-structured contracts allow for flexible termination and offboarding.